Turning Identity Verification into Secure, Trusted Digital Processes
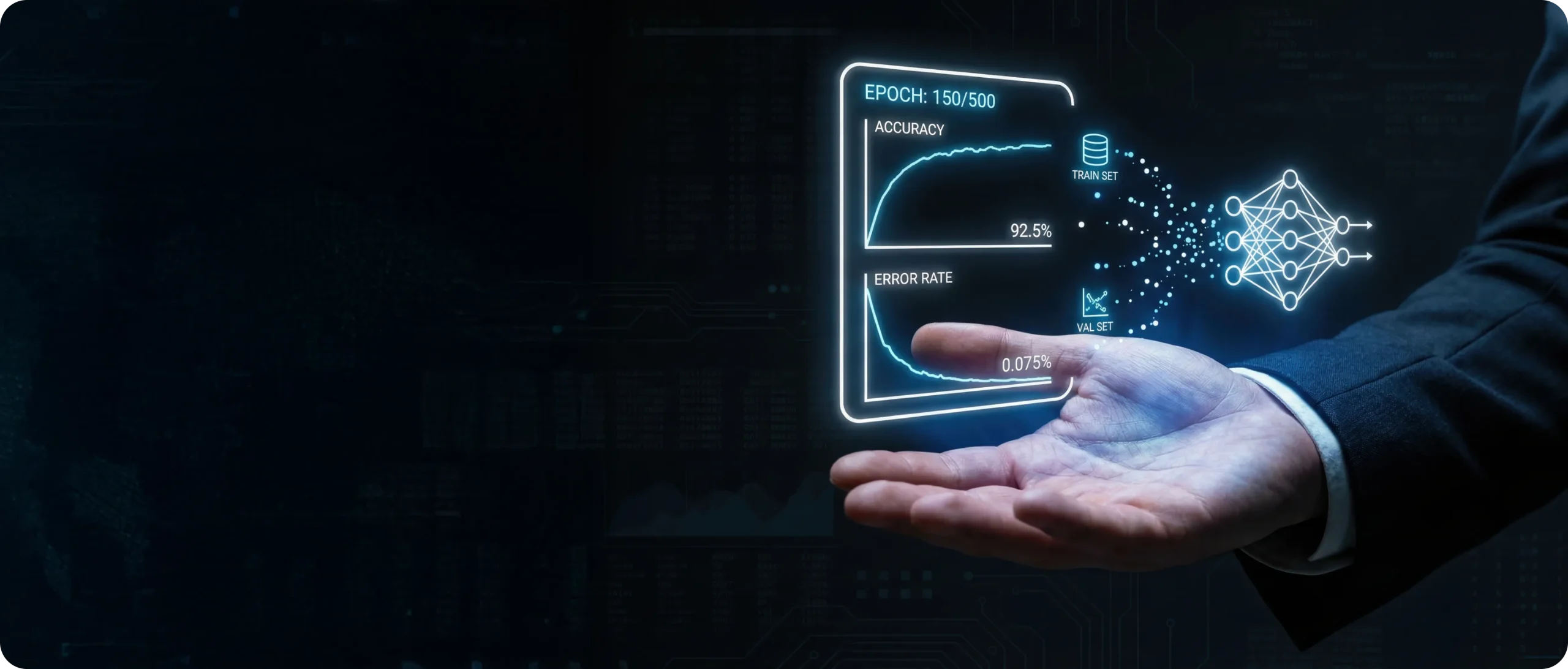
We at Yudiz work with organizations where identity verification is slow, repetitive, and fragmented across platforms. Traditional KYC processes depend on manual checks, duplicated documents, and centralized databases that increase risk, cost, and user friction. This use case focuses on how we build Digital Identity & KYC Systems that simplify verification while maintaining security, privacy, and regulatory alignment.
Through Blockchain Digital Identity, we allow individuals and organizations to verify identity once and reuse it securely across platforms. Verification becomes faster, more reliable, and easier to manage without compromising control over sensitive data.
Get A Quote